- COURSES
- SPECIALS
- BLOG
- MEMBERS
- SHOP
- ABOUT
- ENROLL HERE
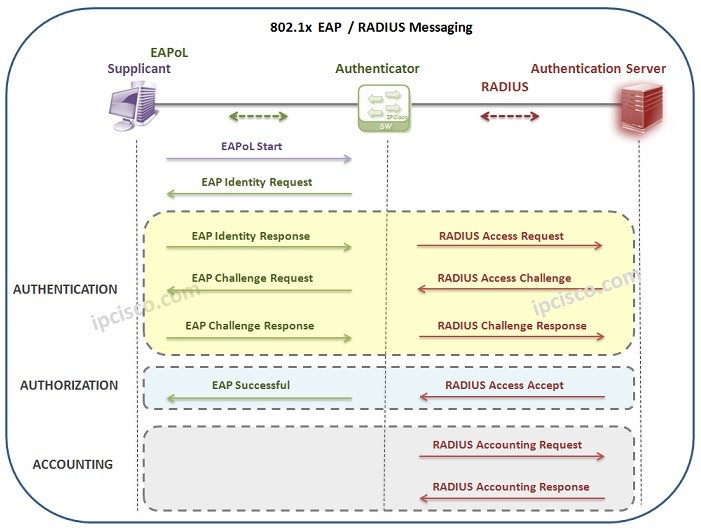
Table of Contents
802.1x is a LAN Security Mechanism that provides port based access control in the network devices. In 802.1x mechanism, devices needs to be authenticated before accessing the network.
In 802.1x mechanism, there are three roles.These 802.1x roles are :
• Supplicant
• Authenticator
• Authentication Server
Supplicant : The device that need to be authenticated before network access
Authenticator : The device that the other devices authentication needed devices are connected. A central point to come together.
Authentication Server : The device that checks the supplicant and provides authentication or not.
Here, let’s go through an example. Think about that you are a new employee in a company and you have just get your laptop. You would like to connect the company’s network. Here, the login client that your company has given to you, is the Supplicant.
• Your Client (Supplicant)
If your company is using 802.1x authentication, it has two main configurations in the company network for network users. These configurations are done by the company it staff to secure company network. These configurations are:
• Switch’s 802.1x Configuration (Authenticator)
• AAA Server Configuration (Authentication Server)
The company switch port that you are connected to, must be configured with 802.1x. Beside, usernames and passwords of the clients(Supplicant), must be defined in the AAA Server.
So, when you try to connect the company’s network, you need to be authenticated. This authentication is done by company’s Authentication Server through the switch (Authenticator) that you are connected to.
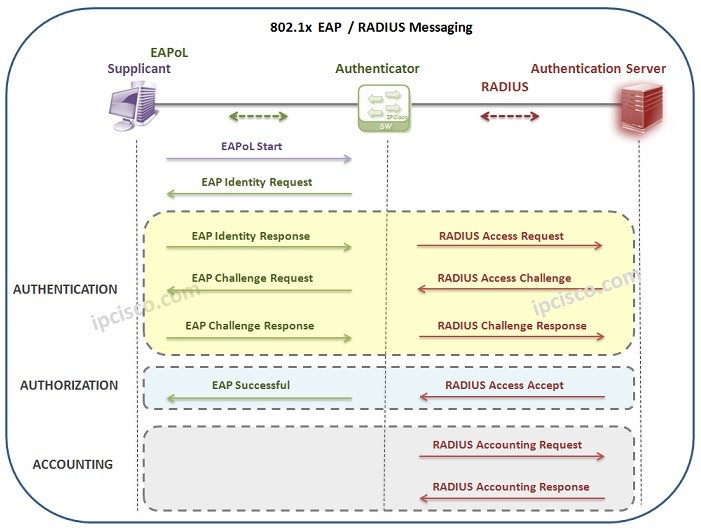
Here the process works like below:
1) Network Connection Request to Authenticator (Switch)
2) Identity Request to Supplicant (Host)
3) User & Password are Sent to Authenticator (Switch)
4) Authentication Check Request to Authentication Server (AAA Server)
5) At Server Authentication will be confirmed and Authorization will be sent to Authenticator (Switch)
There is an Authentication Protocol use with 802.1x that is used between Supplicant (Host) and Authentication Server (AAA Server). The name of this protocol is EAP (Extensible Authentication Protocol) . With EAP, Supplicant and Authenticator determines the Authentication method.
Here, there are different other protocols and encapsulation technologies are used between Supplicant, Authenticator and Authentication Server.
The technology between Supplicant and Authenticator, is Ethernet, a leyer 2 technology. Here, the EAP packets are transfered in ethernet frame with EAP over LAN (EAPol) encapsulation.
The protocols used between Authenticator and Authentication Server are RADIUS or Diameter Protocols.
Now, let’s think about a 802.1x process with RADIUS and check both EAP and RADIUS messages between the three components of 802.1x.
Leave a Reply