- COURSES
- SPECIALS
- BLOG
- MEMBERS
- SHOP
- ABOUT
- ENROLL HERE
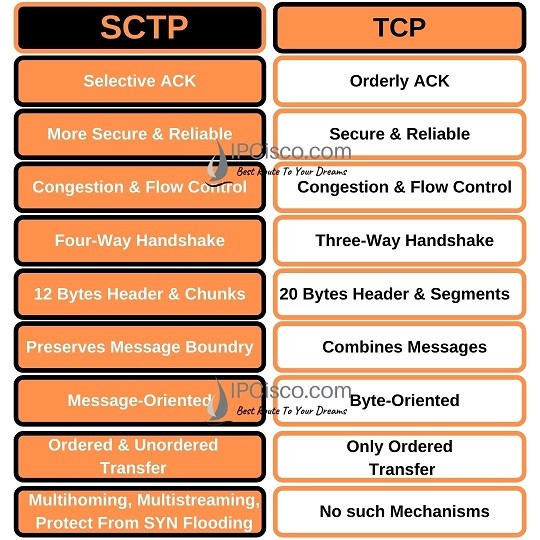
Table of Contents
The basic answer of what is SCTP question is, SCTP (Stream Control Transmission Protocol) is a computer network protocol that works on Transport Layer of the OSI Model and TCP/IP Model. It is basically a transport protocol like TCP and UDP. But it similar and different properties that other transport layer protocols. SCTP Protocol is developed by the Signaling Transport (SIGTRAN) group of IETF (Internet Engineering Task Force). It is mainly developed for Signalling System 7 (SS7) transport over IP-based networks. The details of this protocol is explained in RFC 4960.
First of all, SCTP Protocol is a secure and reliable transport protocol like TCP. Although it inherits many properties of TCP, it has some properties of also UDP. Stream Control Transmission Protocol uses message-oriented feature of UDP and it uses reliable and ordered structure of TCP. It also uses an error-free, non-duplicated secure transfer with the help of checksums, sequence numbers and retransmission mechanism. With congestion control and packet loss detection mechanism, it is very similar to TCP. But it is a different protocol. In the following parts, we will talk about SCTP vs TCP detailly. We will learn the similarities and differences of these two protocols.
Beside inherited properties of TCP, Stream Control Transmission Protocol also has new features that are very useful. For example, Stream Control Transmission Protocol provides validation and acknowledgement mechanism against attacks. It uses notifications for duplicate messages. It supports Multihoming and by doing this provide a redundant network topology. There are more properties that makes SCTP a better protocol than TCP.
Test Yourself With Network Quiz Pages!
After learning what is SCTP, now, let’s focus on SCTP vs TCP. Both SCTP and TCP are Transport layer protocols of OSI Model. So, there are some common parts of these protocols beside their differences. So, what are these similarities and differences if we focus on SCTP vs TCP? Let’s compare these two transport layer protocols and learn SCTP vs TCP detailly.
First of all, let’s start with the similarities of these two network protocols.
Stream Control Transmission Protocol and TCP work on the transport layer of osi reference model. They are transport layer protocols.
Both of these protocols need connection before sending data. They are connection-oriented protocols. They use different steps messaging for session establishment.
Both TCP and SCTP Protocol are secure protocols. They used for the applications that need more security.
TCP and SCTP have Flow Control mechanism beside Congestion Control mechanism. They are reliable protocols.
Now, let’s focus the differences of TCP and SCTP.
Stream Control Transmission Protocol uses Four-Way Handshake while TCP uses Three-Way Handshake during session establishment. And during shut down, this time, Stream Control Transmission Protocol uses Three-Way Handshake and TCP uses Four-Way Handshake.
Stream Control Transmission Protocol supports Multihoming and Multistreaming. There is no support for these in TCP mechanism.
Stream Control Transmission Protocol provides extra security mechanism towards security attempts. It provides towards SYN flooding attacks. There is no mechanism for this in TCP.
In TCP there is only ordered data transfer. But Stream Control Transmission Protocol supports also unordered data transfer beside ordered data transfer.
Stream Control Transmission Protocol is a message-oriented protocol while TCP is a byte-oriented protocol. Data delivery is more flexible with message-oriented system used by SCTP.
In TCP data is represented as Segment while in Stream Control Transmission Protocol it is represented as Chunk.
The header part of TCP is 20 bytes. While Stream Control Transmission Protocol has 12 bytes long header. The checksum part of TCP is 16 bytes and this is 32 bytes for SCTP Checksum.
STCP Packet consist of two main parts as Header and Payload. The Header is common but the Payload consist of variable Chunks. These chunks are used for various purposes.
Common STCP Header is 12 bytes long and it consists of the below parts:
The meaning of these SCTP Header parts are given below:
Source Port shows the sending port.
Destination Port shows the receiving port.
Verification Tag is a 32-bit random value which distinguish the packets form the previous connection.
Checksum is classic CRC32 algorithm to detect erros.
STCP Payload part consist of different STCP Chunks. These chunks have some common parts. These are:
The meanings of these Chunk parts are given below:
Type shows Control or Data Chunk. Type is 1 byte long.
Flags includes various chunk specific bits. Flag part is 1 byte long. There are 8 flag bits.
Length shows size of chunk including chunk header. It is 2 bytes long.
Chunk Value includes chunk specific data.
Below, you can find different Chunks and their roles in SCTP Communication:
DATA Chunk: Carries user data
INIT Chunk: Initiates an association between SCTP endpoints
INIT ACK Chunk: Acknowledges association establishment
SACK Chunk: Acknowledges received DATA chunks and informs the peer endpoint of gaps in the received subsequences of DATA chunks
HEARTBEAT Chunk: Tests the reachability of an Stream Control Transmission Protocol endpoint
HEARTBEAT ACK Chunk: Acknowledges reception of a HEARTBEAT chunk
ABORT Chunk: Forces an immediate close of an association
SHUTDOWN Chunk: Initiates a graceful close of an association
SHUTDOWN ACK Chunk: Acknowledges reception of a SHUTDOWN chunk
ERROR Chunk: Reports various error conditions
COOKIE ECHO Chunk: Used during the association establishment process
COOKIE ACK Chunk: Acknowledges reception of a COOKIE ECHO chunk
SHUTDOWN COMPLETE Chunk: Completes a graceful association close
Like UDP and TCP, SCTP Protocol also uses messages. Before Stream Control Transmission Protocol users can send data each other, SCTP Association must be done. This is like TCP Three-Way Handshake. But Stream Control Transmission Protocol not only consist of three steps but it uses Four steps. This is called SCTP Four-Way Handshake. During SCTP Association, a Cookie mechanism is used against security attacks. So, what are these four messages used in SCTP Association, SCTP Four-Way Handshake. These SCTP messages are given below:
So, let’s explain SCTP Four-Way Handshake mechanism with the above shape.
Here, A sends an SCTP packet that contains INIT Chunk. The other end, B receives this and replies with a packet that contains INIT-ACK Chunk. Both of these Chunks can include one more IP addresses according to the source. With these INIT Chunks, number of outbound streams supported by this association is determined. Beside maximum inbound streams accepted by each end is mentioned.
After these two messages, two additional packets are sent each other to establish the SCTP Protocol Association. These packets are the packets that includes COOKIE ECHO and COOKIE ACK. These messages are used against security attacks.
After the establishment, both ends can send data each other. Stream Control Transmission Protocol mechanism monitors this connection by sending periodic SCTP packets that contain HEARTBEAT Chunks.
How about shutting down this Stream Control Transmission Protocol Association? As you remember, to shut down a TCP connection, we need Four-way Handshake. This time, Stream Control Transmission Protocol need three message and close the connection with three messages. These messages are given below:
There are different key features are coming by using Stream Control Transmission Protocol as transport layer protocol. In this lesson, we will talk about these STP key features. So, what are these features? These are:
Now, let’s learn these key features of SCTP Protocol.
Leave a Reply