- COURSES
- SPECIALS
- BLOG
- MEMBERS
- SHOP
- ABOUT
- ENROLL HERE
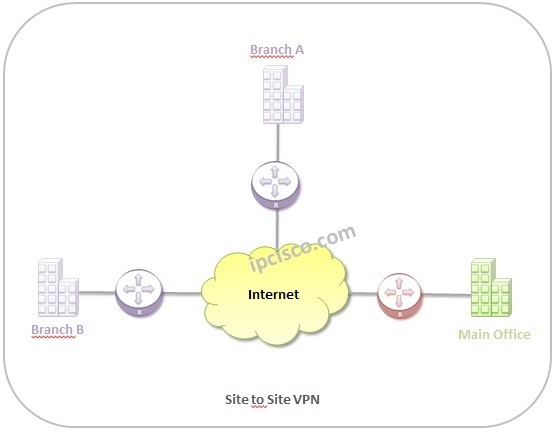
Table of Contents
VPN (Virtual Private Network) is a technology that provides a secure connection to a private network over Internet for users. By encrypting the connections, VPN provides security in this type communication. Basically this security is provided over a VPN Tunnel and provide a trusted connection by avoiding any hacker attacks. Different VPN types and Protocols of VPN provide various secured connections.
There are two main VPN Types. These VPN Types are:
In this lesson, we will learn the types of VPN detailly. Let’s start.
Remote Access VPN is the first of the two VPN types. Remote Access VPN is the VPN type with which, users can access the private networks over internet remotely.
This type of VPN, provides network access chance to remote users, travelling employees, any workers far away from its company. Remote Access VPN is usually used in corporate networks. With Remote Access VPN, users can use their enterprise network’s resources as they are connected directly to their network.
Beside corporate usage, this type of VPN is also used in Home networks. Any users in the home, can use Remote Access VPN to connect internet. By doing this, home users can avoid any regional restrictions like website blocking etc. Beside, home users use it also for a better security during their internet connection.
Site to Site VPN is the VPN type that is used between different locations of companies. With this VPN type company sites which are in geographically different places are connected over internet securily.
There are two diferent sub Site to Site VPN types. These are:
In Intranet Based VPN, the branches of a company is connected over internet as they are in the same network. In this style, there is only one company, its branches and there is no eternal connection.
In Extranet Based VPN, different companies are connected over internet. As the name of the VPN implies, here, each company is connected to an external company.
There are different types of VPN Protocols. With these VPN Protocols, different types of security can be provided. What are these VPN Protocols? These are :
One of the most important Protocols of VPN is IPSec. IPSec for VPN provides Secure Connection over IP networks. With this VPN protocol authentication and encryption are used.
There are different types of IPSec and with this types of IPSec, there are different encryption modes. These are Transport Mode and Tunneling Mode. In transfer mode oly the message in the traffic is encrypted. On the other hand, in tunneling mode, whole data is encrypted.
IPSec is a little difficult to build and it is also expensive solution if you compare with other VPN solutions.
In IPSec Lesson, you can learn this protocol detailly.
Layer 2 Tunneling Protocol (L2TP) is another VPN protocol that is widely used in network World. At the beginning it has many vulnerabilities but after a while it is used with IPSec. IPSec provides extra security to L2TP. Here, the tunnel creation is done by L2TP and the encryptions is done by IPSec.
PPTP is a widely used tunnelling protocol that uses Point-to-Point Protocol (PPP) to encrypt the data through the tunnel. PPTP is a fast protocol if you compare with other tunneling protocols. But it has some vulnerabilities. Over the years, network attacks has increased and this VPN vulnerabilities become important gap. So, even it is a widely used VPN protocol, PPTP is not as secure as other tunneling protocols.
SSTP (Secure Socket Tunneling Protocol) is a VPN solution that came with Windows build in solution for VPN. It is similar to Open VPN but instead of an open solution, it is used on mainly Windows. So, it is not a widely prefered VPN protocol.
Because of the fact that it has developed for Windows, now, it is not used on Linux widely and can not used on Macs.
The security of SSTP (Secure Socket Tunneling Protocol) is like Open VPN but fort his, you shoould trus Windows a little.
Internet Key Exchange version 2 (IKEv2), was developed by Cisco and Microsoft. In real, it is not a VPN protocol. It is used especially for mobile device connections.
IKEv2 is a fast and secure protocol. It uses various encryption mechanims like AES, IPSec etc.
The combination of these two protocols, SSL and TLS build a good VPN solution especially for e-commerce websites. SSL and TLS is used over web browser. Here, your web browser is VPN Client.
This type of VPN is not for home users. It is mainly used on websites that provide shopping service to the customers. With SSL and TLS VPN solution, websites provide secure shopping service to the customers.
Open VPN is an open source and one of the Protocols of VPN that uses Open SSL, TLS protocol. It is a secure VPN protocol that uses many different encryption algorithms.
It is not supported by operations systems. To use Open VPN, you should use a third party program.
Open VPN is not fast like PPTP but, it is almost fast as L2TP. And, Open VPN can be built automatiaclly with third party providers’ applications. It is not a manual solution.
SSH (Secure Shell) is another technique for Protocols of VPN. With SSH VPN, SSH connection is created by SSH Client. The data is transfered over a secured encrypted VPN tunnel.
SSH Works as Client-Server mechanism. The client requests a secure connection and a public key is used between these two ends.
MPLS VPN is the VPN solution that is used by Service Providers. It is the most used VPN types used by Service Providers. MPLS VPN is a complex and expensive solution for home users.
There are different types of MPLS VPNs. Mainly there are two types MPLS VPNs. These are :
Layer 2 VPN has also two sub categories:
Beside, Layer 3 VPNs are also knowns as VPRN.
According to the used technology, there are also different types of Pseudowires (VPWS).
MPLS VPNs has explained detailly in another lessons. You can check MPLS VPN lessons to learn more about them.
Hybrid VPN is a VPN type that provide one more VPN solution inside as its name implies. For example MPLS and IPSec VPNs can be used together inside a Hybrid VPN. This type of VPN is an expensive solution but eliminate one of these protocols disadvantages and use the others advantage together.
Leave a Reply