- COURSES
- SPECIALS
- BLOG
- MEMBERS
- SHOP
- BOOKSHELF
- ABOUT
- ENROLL HERE
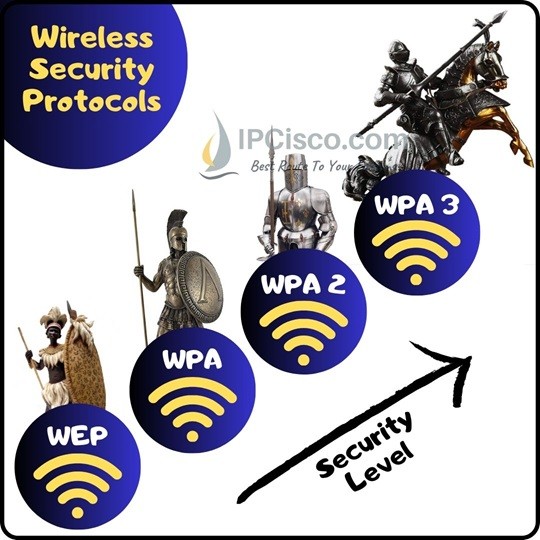
Table of Contents
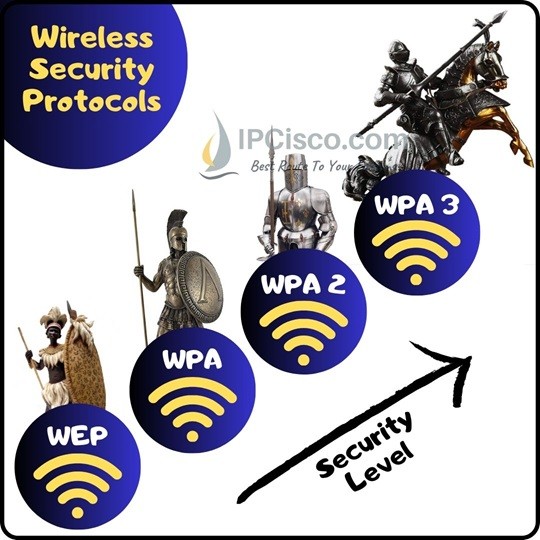
In Wireless LANs, Access Point Passwords are important. But passwords are only the half of the security. Password Encryption is the second half. So, according to used Password Encryption, your system is vulnerable, secured or more secured. To achieve various security levels, different password encryptions are used. So what are these Wireless Security Protocols? These Wireless Security Protocols are WEP, WPA, WPA2 and WPA3.
Now, let’s talk about these Wireless Security Protocols detailly.
You can also check WLC Management Access Connections
WEP (Wired Equivalent Privacy) is the first of Wireless Security Protocols. It has developed at 1999. It was developed to protect the wireless data between Clients and Access Points (APs) towards hackers.
At the beginning maximum 64-bit encryption was allowed in US. So, WEP was using 64-bit encryption. After the restrictions, 128-bit and 256-bit WEP has developed.
WEP was widely used but it has too vulnerable to the password hacks. Cybersecurity experts detect many vulnerabilities of this first Wireless Security Protocol. So, Wi-Fi Alliance retired it offically at 2004. For today’s World WEP (Wired Equivalent Privacy) is not a secure protocol and it is outdated.
Wi-Fi Protected Access (WPA) was developed at 2003 by Wi-Fi Alliance. Because of the vulnerabilities of WEP, a new protocol must be developed. It is done with Wi-Fi Protected Access (WPA). WPA was using 256-bit WPA-PSK (Pre-Shared Key).
With WPA, some additional security mechanisms has developed. Two of these new security mechanisms are “Message Integrity Check” and “Temporal Key Integrity Protocol (TKIP)”. With Message Integrity Check mechanism, the message content became more secure towards hackers. With TKIP, key system had changed top Per-Packet. After a while instead of TKIP, AES (Advanced Encryption Standard) would be used.
There was two different modes of WPA. One of these WPA modes is used for Enterprises and the other is used for Individuals. These WPA Modes are:
Enterprise Mode, WPA-EAP was used for Enterprises. It was used with Extensible Authentication Protocol (EAP) and because of this it was more secured. WPA Enterprise mode was needed an Authentication Server.
Personal Mode, WPA-PSK was used for Individuals. Pre shared keys was used with this mode. The implementation and management of this mode was easier.
Althought WPA is more secure then WEP, it was not enought. Different security vulnerabilities was detected on Wi-Fi Protected Access (WPA).
WPA2 (Wi-Fi Protected Access 2) has developed at 2006. It was advanced version of first WPA. Vulnerable parts of WPA become stronger with WPA2.
WPA2 offered new encryption and authentication mechanisms to provide more secured networks. These mechanisms was AES (Advanced Encryption Standard) and CCMP (Counter Cipher Mode with Block Chaining Message Authentication Code Protocol). These mechanisms was being used instead of previous mechanism TKIP. For interoparability, TKIP was also used but as a fallback.
AES (Advanced Encryption Standard) had improved by United States Goverment. The main aim of this protocols was encrypting the top secret information. After a while, it is thought that using AES on small networks could also improve the security. And it is.
What is more with WPA2? There are also other improvements. For example, Clients can move from one Access Point to another Access Point with no reauthentication. Pre authentication or Pairwise Master Key can be used for this.
WPA2 can be good for Home networks but it is vulnerable for Enterprise networks. Because, attackers can have access to the network secured with WPA2. After accessing the network they can access passwords. Dictionaty Attacks are the most vulnerable part of WPA2 for passwords.
The last developed Security Standard for Wireless is WPA3 (Wi-Fi Protected Access 3). WPA3 offers improved authentication and encryption. It will be used more with 802.11ax standard. WPA3 will be mandatory with Wi-Fi 6.
With Wi-Fi 6, better security will be needed and there will be more wireless devices. So, with these requirements security will become more important and WPA3 will be used with Wi-Fi 6.
There is also another improvement with this WPA3. This is OWE (Opportunistic Wireless Encryption). OWE is a technology that is developed for Public Networks. With this technology, auto encryption will be done without user intervention. Think about this. You are in Starbucks and working with your PC. With WPA2, any attacker in the same public place with you, can do a Man-in-the-Middle attack towards your system. They can start a Dictionary Attack for your password. With WPA3, it is prevented.
WPA2 is vulnerable to Dictionary Attacks that is used to predict password with many different attempts. Hackers can do this atteck even if they are not in the same network with the victim. To prohibit this type of attack, WPA3 offers a new Key Exchange Protocol. With this protocol, it will use a secure way, Simultaneous Authentication of Equal handshake. Before, with WPA2, Four way Handshake was being used and this is vulnerable.
WPA3 provide extra security and encryption if you compare with WPA2. With WPA3, all the traffic between you and and the other end will be encrypted, till the other end authenticated.
There is also another new connection type that is coming with WPA3. With this new type, you can use th QR Codes to connect the devices to the networks. For example, you can use your smart phone to scan the QR Codes of Printers, Access Points etc and you are connected after that to the access point,printer sor any ot devcei that will be in our lives with Internet of Things (IoT). This type of communication will require extra security. So, WPA3 is a good solution for this.
You can find a good comparison table for WEP, WPA, WPA2 and WPA3. In this table, you can find all the key differences of these Wireless Security Protocols
a) WEP
b) WPA
c) WPA 2
d) WPA 3
a) Wireless Public Access
b) Wireless Port Access
c) Wi-Fi Protected Access
d) Wi-Fi Packet Access
a) WEP
b) WPA
c) WPA 2
d) WPA 3
a) Wired Equivalent Privacy
b) Wi-Fi Protected Access
c) Wi-Fi Protected Access 2
d) Wi-Fi Protected Access 3
a) WEP
b) WPA
c) WPA 2
d) WPA 3
Leave a Reply